API Reference
REST API authentication, base URL, pagination, and the full OpenAPI reference for the Stealed leak search and verification endpoints.
The Stealed public API exposes read-only leak search and verification endpoints. Management operations (monitors, channels, domains, keywords, team members) stay scoped to the dashboard with an authenticated user session.
Base URL
https://api.stealed.ioAll endpoints are HTTPS only. HTTP is rejected.
Authentication
Every request carries an API key in the X-Api-Key header.
curl -H "X-Api-Key: $STEALED_API_KEY" \
https://api.stealed.io/leaks/meCreating an API key
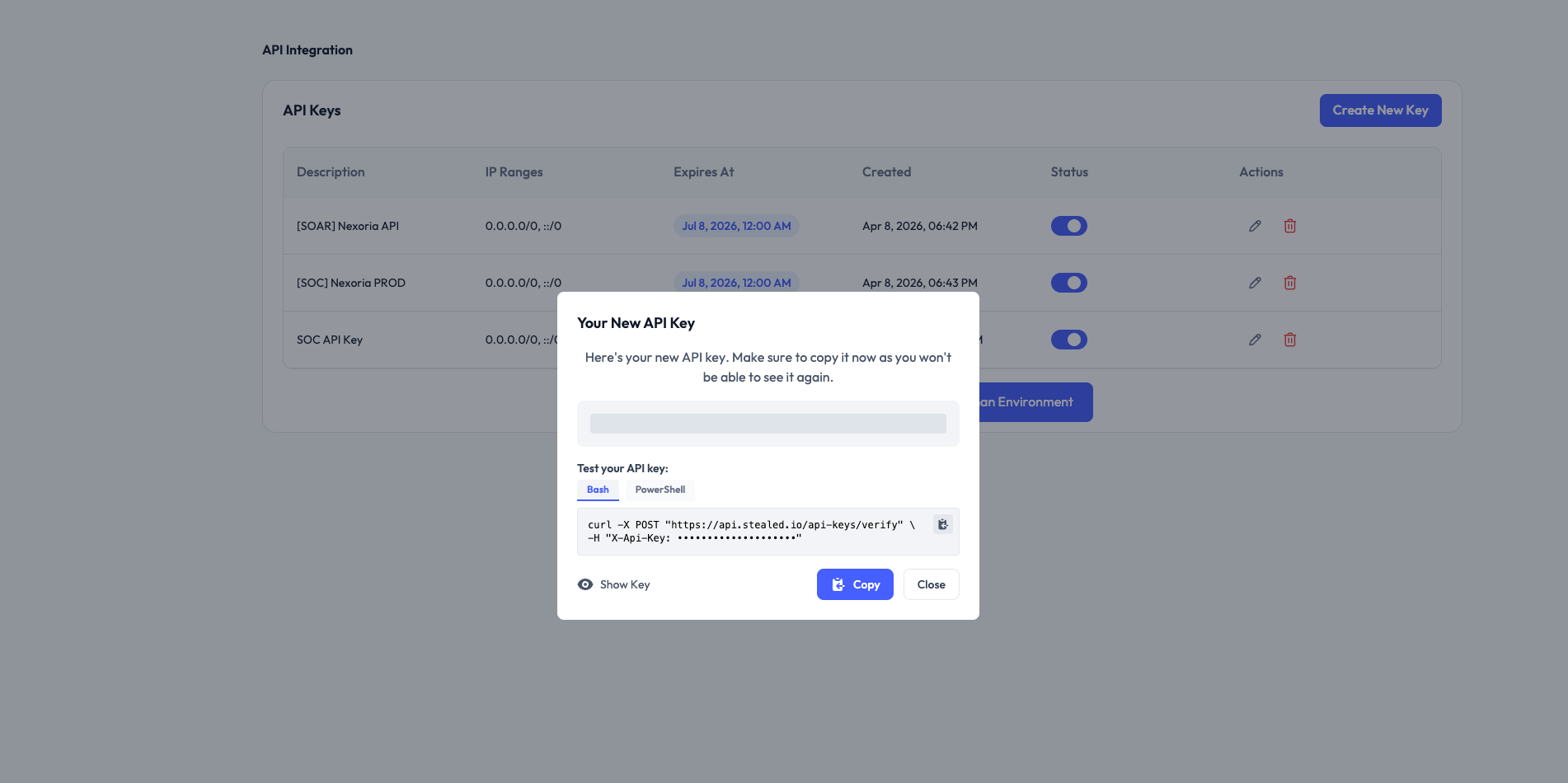
API keys are organization-scoped. To create one:
- Open the dashboard at app.stealed.io.
- Go to Settings → API Integration.
- Click New API key, give it a descriptive name (e.g. "splunk ingestion") and click Create.
- Copy the key immediately. The full secret is shown only once. After that you can see the prefix in the dashboard but not the full value.
Permissions
A key grants access to:
GET /leaks/*: leak search, statistics, keyword search.POST /api-keys/verify: validate a key and read the organization metadata.
Management endpoints (monitors, channels, domains, keywords, team, API keys CRUD) are NOT in the public API surface. They require a user session in the dashboard.
Rotating a key
To rotate, create a new key, deploy it to your integration, then delete the old one from the dashboard. Keys take effect immediately on creation and are invalidated immediately on deletion.
Revoking a leaked key
Suspect a key has been leaked? Delete it from Settings → API Integration. The deletion is effective immediately for new requests. Already-in-flight requests with that key complete normally.
Pagination
The /leaks/details endpoint returns paginated results:
{
"data": [...],
"total": 12345,
"page": 1,
"page_size": 50,
"total_pages": 247
}- Default
page_size: 50 - Maximum
page_size: 200 - Pagination is offset-based, not cursor-based; for very large exports,
bound your queries with
start_dateandend_daterather than paging through millions of rows.
Time window
The /leaks/* endpoints default to the last 14 days when neither
start_date nor end_date is provided. Format: YYYY-MM-DD. Both
parameters can be specified independently.
Rate limits
Per API key:
- 60 requests / minute (burst tolerated up to 100)
- 5,000 requests / hour
- 100,000 requests / day
When you hit a limit, the API returns 429 Too Many Requests with a
Retry-After header (in seconds). Back off and retry.
Errors
Errors follow RFC 9457 Problem Details:
{
"type": "https://api.stealed.io/errors/invalid-domain",
"title": "Invalid domain",
"status": 400,
"detail": "The domain 'acme' is not in your watchlist.",
"instance": "/leaks/details"
}Common HTTP statuses:
| Status | Meaning |
|---|---|
| 200 | Success |
| 400 | Validation error (see detail) |
| 401 | Missing or invalid API key |
| 403 | Key valid but doesn't authorize this operation |
| 404 | Resource not found |
| 429 | Rate limit exceeded |
| 500 | Internal error: retry with exponential backoff |
Endpoint reference
The full OpenAPI reference (with schemas, parameters and try-it-now) is generated below from the live spec. Each operation has its own page.
The OpenAPI spec is also available at api.stealed.io/openapi.json for codegen and SDK generation.
Mute a monitor
Silence a monitor for a defined window without losing its state. Useful for maintenance windows or active triage.
[Deprecated] Retrieve leaks for the current user/organization for a given query GET
**Deprecated**: For leak details, use `GET /leaks/details` which provides pagination, deduplication, search, and sorting. For keyword search, use `GET /leaks/keyword/search`. Retrieve leak statistics for the current organization. Each call returns a single statistic based on the `query` parameter. Both `query` and `identifier_column` are **required**. If `start_date` and `end_date` are not provided, defaults to **the last 14 days**. **Required Parameters:** - `query`: The statistic to retrieve (see query types below) - `identifier_column`: `root_domain`, `email_domain`, or `username` **Available Query Types:** **Generic Queries (counts and aggregates):** - `generic_total_leaks_count`: Total leaks count - `generic_uniq_username_count`: Unique usernames detected - `generic_uniq_source_count`: Unique sources with at least one detection - `generic_uniq_password_count`: Unique passwords detected - `generic_uniq_domain_count`: Unique domains detected - `generic_uniq_leaks_count`: Unique leaks (by hash) - `generic_latest_leak_date`: Date of the latest leak - `generic_reused_password_count`: Passwords reused across multiple domains - `generic_password_strength`: Average password length **Generic Queries (detailed data):** - `generic_leaks_type_by_identifier`: Leaks grouped by type (combo/stealer) - `generic_leaks_by_day`: Leaks per day - `generic_password_per_length_per_identifier`: Password distribution by length - `generic_most_recent_leaks_by_identifier`: Most recent leaks **Organization Queries:** - `org_uniq_priv_account_count`: Privileged accounts leaked (admin, root, etc.) - `org_detailed_uniq_admin_account_count`: Detailed list of admin accounts - `org_uniq_ext_account_count`: External accounts count - `org_detailed_uniq_ext_account_count`: Detailed list of external accounts - `org_detailed_uniq_username_count`: Detailed list of all usernames - `org_total_leaks_count_group_by_identifier`: Leaks grouped by identifier - `org_total_leaks_count_group_by_domain`: Leaks grouped by domain - `org_total_leaks_count_group_by_email_domain`: Leaks grouped by email domain - `org_total_leaks_count_group_by_root_domain`: Leaks grouped by root domain - `org_top_domain_leaks_by_identifier`: Top domains by leak count - `org_top_user_leaks_by_identifier`: Top users by leak count - `org_leaks_detail_per_identifier`: Full leak details per identifier **Examples:** ```bash # Total leaks count GET /leaks/me?query=generic_total_leaks_count&identifier_column=root_domain # Unique usernames GET /leaks/me?query=generic_uniq_username_count&identifier_column=root_domain # Stealer leaks only GET /leaks/me?query=generic_total_leaks_count&identifier_column=root_domain&type=Stealer # Leaks per day with date range GET /leaks/me?query=generic_leaks_by_day&identifier_column=root_domain&start_date=2025-01-01&end_date=2025-01-31 # Leaks grouped by domain, limited to 100 GET /leaks/me?query=org_total_leaks_count_group_by_domain&identifier_column=root_domain&limit=100 # Multiple domain filter GET /leaks/me?query=org_total_leaks_count_group_by_domain&identifier_column=root_domain&domain=test.example.com&domain=monitoring.example.com ```