What is Stealed?
A real-time credential leak detection platform that monitors infostealer logs, underground forums and private Telegram channels.
Stealed is a B2B SaaS built for security teams who need to know, in real time, when their organization's credentials end up in the hands of cybercriminals. It continuously monitors infostealer malware logs, underground forums and private Telegram channels to detect compromised credentials the moment they start circulating.
The problem Stealed solves
Traditional breach-notification services like HaveIBeenPwned alert you after a data breach has been made public. By the time you get notified, the leak may already be weeks or months old, and the credentials may have been exploited long before.
Infostealer malware is a different and far more immediate threat. Families like Redline, Raccoon, Vidar and Lumma silently collect credentials stored on infected machines and exfiltrate them to command-and-control servers. The stolen credentials, often called "logs", are then sold or shared on cybercriminal forums and Telegram channels, sometimes only hours after the theft.
Each infostealer log typically contains:
- Full credentials: URLs, usernames and plaintext passwords pulled from browsers and apps
- Session data: cookies and tokens enabling session hijacking
- Machine metadata: hostname, hardware ID, IP address and geolocation
- Software context: the browser or app the credential was stored in
This level of detail makes infostealer logs far more dangerous than classic breach databases. They give attackers everything they need to log in cleanly, without triggering brute-force alarms or anomaly detection.
How Stealed works
Stealed runs four pipelines in parallel:
- Collection. A distributed crawler ingests data from over 500 sources: underground markets, private Telegram channels, infostealer log dumps, underground forums, paste sites.
- Parsing & indexing. Raw dumps are normalized, deduplicated and indexed in real time. Hashes prevent counting the same credential twice.
- Matching. Your monitors evaluate every incoming leak against your surveillance rules (domains, subdomains, keywords).
- Alerting. When a monitor matches, an event is created and notifications are dispatched to the channels you configured (Slack, Microsoft Teams, webhook, email).
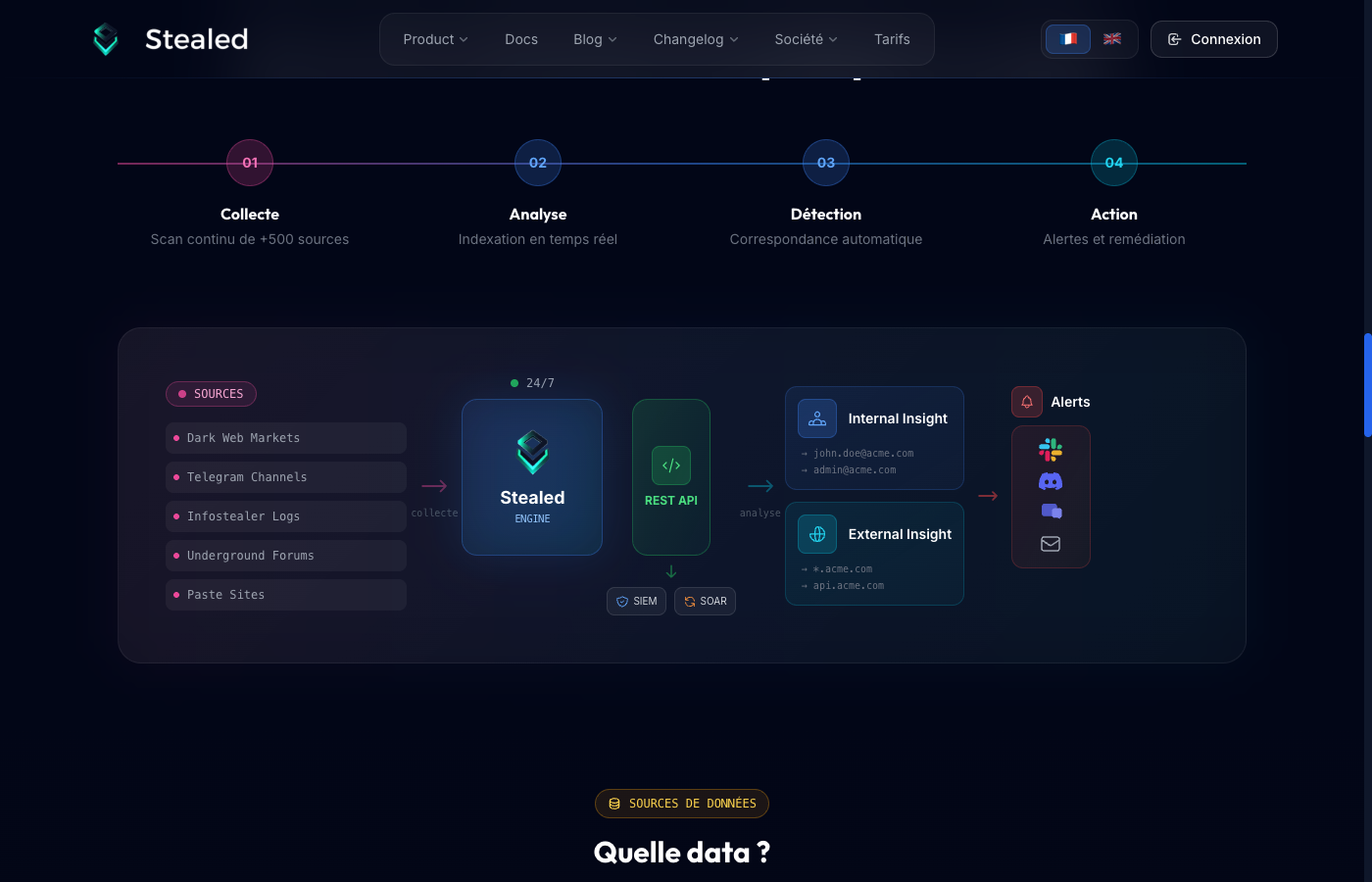
The Stealed dashboard exposes three complementary perspectives on the data: Internal Insight (your collaborators' compromised credentials), External Insight (credentials targeting your public services) and Keyword Insight (mentions of monitored keywords across third-party URLs). See the Surveillance section for details.
Multi-tenant architecture
Stealed is multi-tenant by design. Each organization gets its own logical isolation: dedicated ClickHouse views, scoped API keys, independent monitors and channels. Data from one organization is never visible to another, even internally on the platform.
For MSP / MSSP plans, a parent organization can manage multiple client organizations from a single dashboard while keeping each client's data isolated.
Data sovereignty
Stealed is a French company hosted on Scaleway infrastructure (ISO 27001 + SOC 2). All ingested data and customer metadata stay in EU data centers. No data is sent to the United States, and the credential storage uses hashes suitable for RGPD compliance: only the cryptographic fingerprint of the password is stored, not the plaintext, except where explicit access is granted to your organization for verification.
Regulatory alignment
Stealed delivers capabilities that map directly to several recurring requirements in EU cybersecurity regulations:
- NIS2 (Directive (EU) 2022/2555): risk management, incident handling, incident notification within 24h / 72h. Stealed's monitoring + activity timeline produce the audit trail required by Article 23.
- DORA: ICT-related incident reporting and threat intelligence sharing for financial entities.
- CRA: monitoring of vulnerabilities affecting digital products.
The Monitoring section explains how the activity timeline is exported as an audit trail.
Next steps
- Quickstart: get to your first detected leak in 5 minutes.
- Onboarding guide: full walkthrough: domains, keywords, team, first monitor.